How Quantum Computing Will Impact Cryptography Systems
Quantum computing is emerging as one of the most transformative technologies of the twenty first century. While its potential benefits include breakthroughs in medicine, materials science, and logistics optimization, one of its most significant consequences will affect cryptography systems that currently protect digital communications worldwide. Governments, financial institutions, technology companies, and cybersecurity experts are already preparing for changes that quantum computing may bring to encryption standards.
Understanding how quantum computing interacts with modern cryptography helps organizations anticipate risks and prepare secure systems for the future.
Understanding the Foundations of Modern Cryptography
Modern cryptography protects digital information through mathematical algorithms designed to make unauthorized access extremely difficult. These systems secure online banking, email communication, cloud storage, messaging platforms, and government infrastructure.
Common cryptographic methods include:
- Symmetric encryption algorithms
- Public key cryptography
- Digital signatures
- Hash functions
Public key cryptography is especially important because it enables secure communication between parties who have never met before. Many current encryption standards rely on mathematical problems that are extremely difficult for traditional computers to solve efficiently.
These protections have remained reliable for decades because classical computing systems cannot break them within realistic time limits.
What Makes Quantum Computing Different from Classical Computing
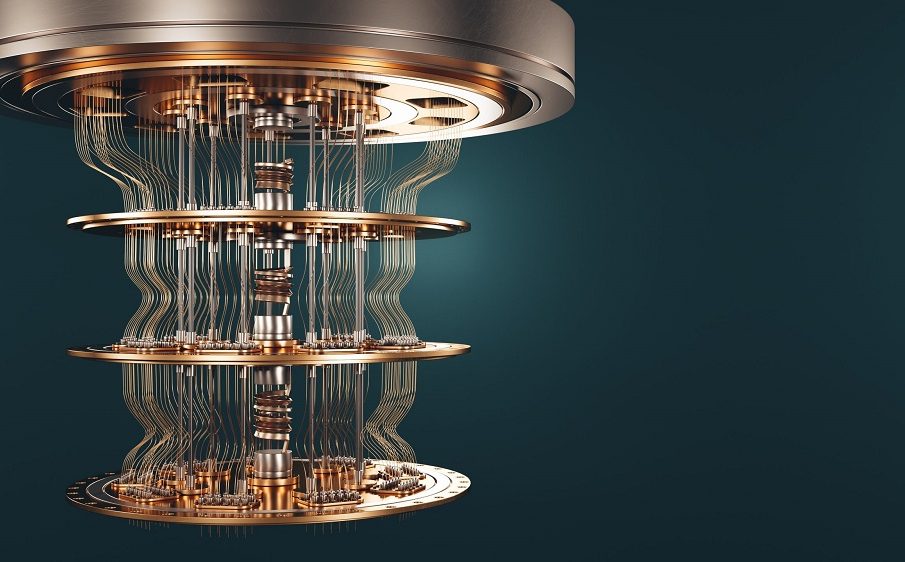
Traditional computers process information using binary bits that represent either zero or one. Quantum computers use qubits, which can represent multiple states simultaneously through a property known as superposition.
Additional quantum characteristics include:
- Superposition allowing multiple calculations at once
- Entanglement linking qubits across distances
- Quantum interference improving computational accuracy
These properties allow quantum computers to perform certain calculations exponentially faster than classical machines.
While quantum computers are still developing, researchers expect them to eventually solve mathematical problems that currently protect encrypted systems.
Why Current Encryption Methods May Become Vulnerable
Many widely used encryption systems depend on the difficulty of factoring large numbers or solving discrete logarithm problems. Classical computers require enormous time to complete these calculations.
Quantum computing changes this assumption.
Certain quantum algorithms can solve these problems much faster, which creates risks for widely deployed encryption standards.
Encryption systems potentially affected include:
- RSA encryption
- Diffie Hellman key exchange
- Elliptic curve cryptography
These methods currently secure financial transactions, secure websites, messaging platforms, and identity verification systems.
Once powerful quantum computers become available at scale, these encryption methods may no longer provide adequate protection.
The Role of Shor Algorithm in Breaking Public Key Encryption
One of the most important discoveries in quantum computing research is the development of Shor algorithm. This quantum algorithm can factor large numbers efficiently, which threatens encryption methods that rely on factoring complexity.
Public key encryption systems rely heavily on the assumption that factoring large integers is computationally impractical.
Quantum computing challenges that assumption by:
- Reducing computation time dramatically
- Enabling faster number decomposition
- Weakening security assumptions used in key generation
This makes Shor algorithm one of the primary reasons cybersecurity experts are preparing for post quantum cryptographic systems.
How Quantum Computing Affects Symmetric Encryption Systems
Symmetric encryption systems are less vulnerable than public key systems but still affected by quantum computing advances.
Quantum algorithms such as Grover algorithm can reduce the time required to search encryption keys.
Although symmetric encryption remains stronger against quantum attacks compared to public key encryption, organizations may still need adjustments such as:
- Increasing key lengths
- Updating encryption protocols
- Strengthening authentication layers
These measures help maintain security even in a quantum capable environment.
The Emergence of Post Quantum Cryptography
Post quantum cryptography refers to encryption methods designed to remain secure even against quantum computer attacks. Researchers worldwide are developing new algorithms that resist quantum based threats.
These systems rely on mathematical problems believed to be resistant to quantum acceleration.
Examples include:
- Lattice based cryptography
- Hash based cryptography
- Code based cryptography
- Multivariate polynomial cryptography
These approaches provide alternative foundations for secure communication that do not depend on factorization difficulty.
Organizations are gradually preparing to transition toward these new encryption methods.
Why Governments Are Preparing for Quantum Resistant Security
Government agencies manage sensitive data related to national security, defense infrastructure, and intelligence operations. Because this information must remain confidential for decades, preparing for quantum resistant encryption is a priority.
Preparation strategies often include:
- Research funding for secure algorithms
- Migration planning for encryption upgrades
- Collaboration with academic institutions
- Monitoring quantum hardware progress
Long term data protection requires encryption systems capable of resisting future computing capabilities.
The Risk of Harvest Now Decrypt Later Attacks
One major concern related to quantum computing is the possibility of harvest now decrypt later attacks. In this scenario, attackers collect encrypted data today and store it until quantum computers become powerful enough to decrypt it in the future.
Sensitive information at risk includes:
- Government communications
- Financial records
- Healthcare data
- Corporate intellectual property
Organizations handling long term confidential information must prepare for these risks well before large scale quantum systems become available.
Transitioning early to quantum resistant encryption reduces long term exposure.
How Financial Institutions Are Responding to Quantum Threats
Banks and payment networks depend heavily on encryption for secure transactions and identity verification. Because financial systems operate globally and continuously, encryption transitions require careful planning.
Financial institutions are currently focusing on:
- Evaluating cryptographic inventory
- Testing quantum resistant algorithms
- Updating authentication infrastructure
- Coordinating with regulatory agencies
These preparations help maintain trust in digital financial systems during technological transitions.
Cloud Security in a Quantum Computing Era
Cloud platforms store large amounts of personal and enterprise data. As quantum computing evolves, cloud providers must update encryption frameworks to maintain strong protection standards.
Key areas of preparation include:
- Secure key management systems
- Post quantum encryption testing
- Hybrid cryptographic deployments
- Data lifecycle protection planning
Cloud providers play a critical role in shaping how quickly secure encryption transitions occur worldwide.
The Role of Technology Companies in Encryption Migration
Major technology companies develop operating systems, communication platforms, and web infrastructure used globally. Their participation is essential for implementing secure cryptographic upgrades.
Technology companies contribute through:
- Developing quantum resistant protocols
- Supporting software compatibility updates
- Testing performance efficiency
- Collaborating with security researchers
These efforts help ensure encryption transitions remain smooth for everyday users.
Challenges in Transitioning to Quantum Safe Cryptography
Migrating global encryption infrastructure is complex and requires coordination across industries.
Challenges include:
- Compatibility with legacy systems
- Performance tradeoffs in new algorithms
- Implementation costs
- Training cybersecurity professionals
- Standardization across platforms
Despite these challenges, early preparation reduces disruption risks.
Organizations that begin migration planning sooner are better positioned for long term security stability.
Opportunities Created by Quantum Safe Encryption Innovation
Although quantum computing introduces risks to traditional cryptography systems, it also creates opportunities for innovation in cybersecurity research.
New developments include:
- Stronger authentication frameworks
- Advanced identity verification systems
- Improved secure communication protocols
- Long term archival encryption protection
These improvements strengthen digital infrastructure beyond current security capabilities.
Preparing for quantum safe encryption ultimately supports a more resilient cybersecurity environment.
The Timeline for Quantum Computing Impact on Cryptography
Quantum computing capable of breaking widely used encryption standards has not yet reached practical deployment scale. However, research progress continues steadily.
Security experts generally agree that organizations should begin preparing now because encryption transitions require years of planning and testing.
Proactive preparation ensures systems remain protected as computing technology evolves.
Forward looking cybersecurity strategies help maintain trust across digital communication networks worldwide.
FAQ Section
What industries are most affected by quantum computing related cryptography risks
Industries handling sensitive long term data such as finance, healthcare, government, defense, and telecommunications face the greatest impact from quantum related encryption challenges.
Will quantum computing immediately break all existing encryption systems
Quantum computers capable of breaking current encryption standards are still under development, but preparation is necessary because migration timelines are long.
Are personal messaging applications affected by quantum cryptography concerns
Messaging platforms using public key encryption may require future updates to maintain security against quantum capable threats.
Can smaller organizations prepare for quantum safe encryption transitions
Yes smaller organizations can begin by identifying where encryption is used in their systems and adopting updated cryptographic libraries as they become available.
Does quantum computing improve cybersecurity in any way
Quantum technology may support stronger encryption techniques and improved secure communication methods once quantum resistant protocols become widely adopted.
Are password based authentication systems affected by quantum computing
Password systems themselves are less affected directly, but the encryption protecting stored credentials may require strengthening in future security frameworks.
How long does it typically take to replace encryption systems across organizations
Encryption migration timelines vary widely depending on infrastructure complexity, but large scale transitions often require several years of planning and deployment.










